Multiple Severe Vulnerabilities in MonkeyType.Com Chat Based XSS, Auth bypass, User Spoofing - Write-ups and Disclosures - @disclose_io Community Forum
Por um escritor misterioso
Descrição
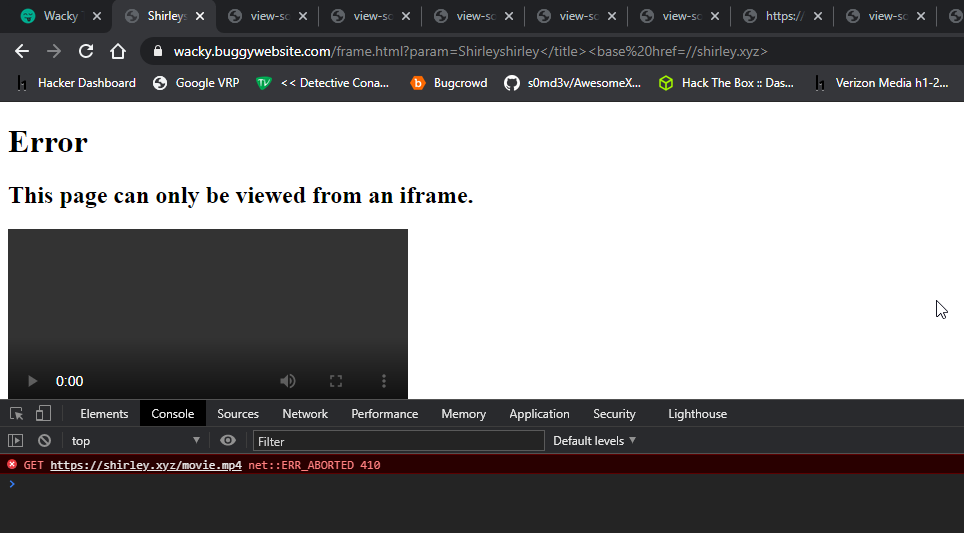
I published the original article over at my independent research project obsrva.org Executive Overview In May 2021, independent security researcher Tyler Butler found several critical vulnerabilities in monkeytype.com, a popular open-source typing-test application with a booming community of over 100k daily unique visitors. The vulnerabilities included stored cross-site scripting and user impersonation in the tribe chat room feature, as well as an authentication bypass vulnerability enablin
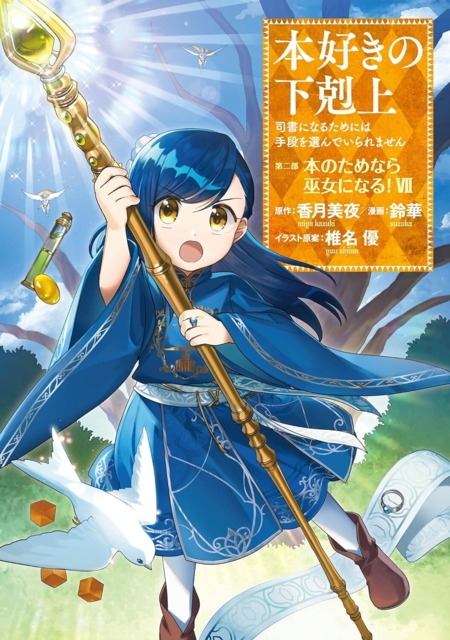
Solving BugPoc XSS challenge. Heyy Everyoneee,, by Sudhanshu Rajbhar
All Vulnerabilities for papyrefb3jewa7fdbakdomx2pj576w7u25fk3kjk6gyyuofz5awcu4id.tor2web.it Patched via Open Bug Bounty
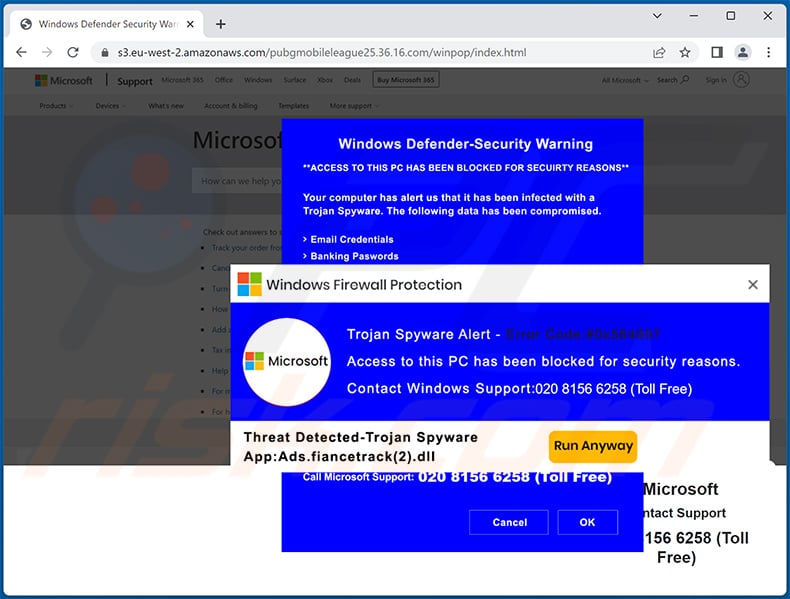
Error Code: #0x564897 POP-UP Scam - Removal and recovery steps (updated)

MX injection and type juggling vulnerabilities · Issue #6229 · roundcube/roundcubemail · GitHub

Bad Request with Ocelot ReRoute using Eureka as Service Provider at LocalHost · Issue #1053 · ThreeMammals/Ocelot · GitHub
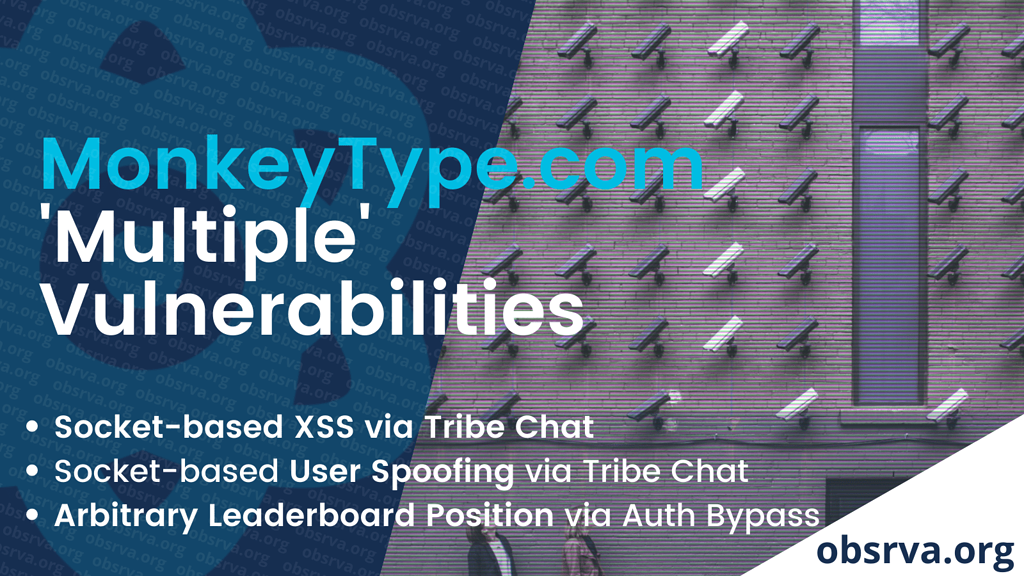
Multiple Severe Vulnerabilities in MonkeyType.Com Chat Based XSS, Auth bypass, User Spoofing - Write-ups and Disclosures - @disclose_io Community Forum
400 Bad requests (such as malformed URIs) do not make it past Tomcat and display a stacktrace in the browser · Issue #21742 · dotCMS/core · GitHub

Hacking_SharePoint_FINAL
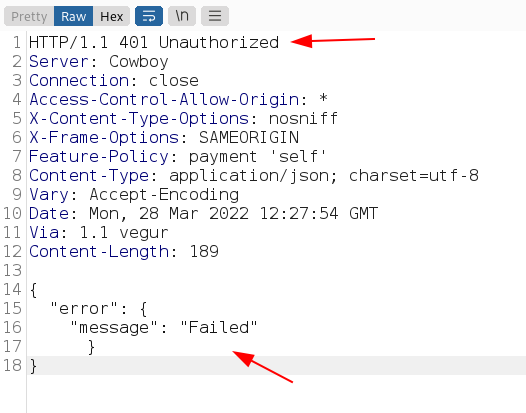
Improper Authorization. This blog will demonstrate an…, by PSDooM
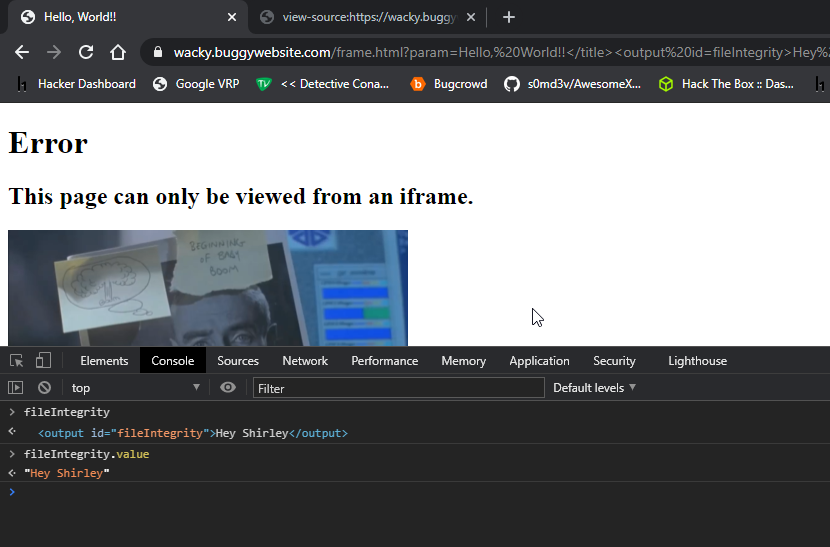
Solving BugPoc XSS challenge. Heyy Everyoneee,, by Sudhanshu Rajbhar
de
por adulto (o preço varia de acordo com o tamanho do grupo)